What is the problem for the operator? – Flubot and Smishing Solutions Part 4/7

What do FluBot and SMS phishing have in common? Shocking daily headlines, the Wild West of URLs, and one easy solution to stop both in their tracks.
If you have heard anything about the newest Flubot attack, you have probably also warned your parents and others not to trust or click any link from an SMS message. This is bad news for MNOs. Fraud has been on a steep incline since the COVID-19 pandemic began, and consumers, while under attack from the virus, are also under attack electronically and financially.
Smishing, malware, and the Flubot are dominating headlines. These attacks may seem like separate threats, but they have a lot in common: They both begin with an SMS message and end in devastating financial losses to subscribers. Mobile operators have responded by issuing warnings to consumers, yet they are missing an enormous opportunity to save the day and savour the glory (and press coverage) any hero should.
What is the problem for the operator?
News and Accountability

The most immediate concern is the current news cycle. The old adage that there is no such thing as bad press does not hold true when it comes to grandma losing her life savings to fraud. When fraud or security breaches are exposed on a single network, we know that all operators are likely at risk of a similar fate.
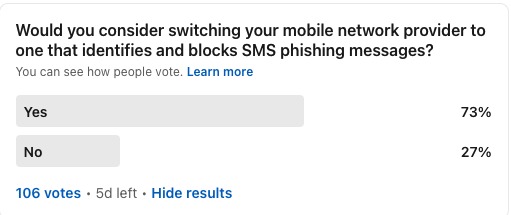
We can predict that the illusion of protecting subscribers through warnings and tweets will not last. Android remains an easy scapegoat only because of its juxtaposition to the iPhone, which has no such loophole. As long as all networks allow this problem to continue, network insecurity is seen not as a loophole, but just the status quo. The public might wonder if SMS, by nature, can even be secured by the operator. It will, however, only take one network publicly and visibly ending this problem for subscribers to demand more from their own mobile networks.
DoS and A2P
Flubot carries the added threat of denial of service if it is able to send SMS messages unchecked by users, handsets, and the network itself. Proofpoint estimates malicious SMS messages to be in the tens of thousands per hour in the UK alone. This is no small concern, yet the threat we should all be concerned about – as an industry – is the slow and steady destruction of SMS and A2P as a revenue stream.
Precaution is also catching. As we have seen in the response to the COVID pandemic, where precaution abounds, so do economic impacts, and for mobile networks, the economy in question is their own. As people exercise greater caution with SMS messages, networks stand to lose untold millions if not billions in lost SMS traffic, and especially lucrative A2P traffic. A2P messaging is a $43 billion business. When we see networks actively and desperately warning their customers to distrust SMS, they are, to an extent, sealing their own fate.
As more and more operators release official statements warning subscribers not to click on any “suspicious” link in any “suspicious SMS”, the more SMS becomes synonymous with “untrusted”. The average person quickly recognises the limits of their expertise in fraud detection which results in people choosing not to open any SMS or clicking on any link from an SMS — to be on the safe side. SMS itself falls under a veil of suspicion, which has repercussions on lucrative A2P SMS volumes. It is difficult to imagine DHL and other companies who have been targeted and imitated ever again expecting their customers to trust an SMS from them, and that is only the tip of the iceberg.
More information on the Cellusys SMS Anti-Phishing Solution
How SMS Anti-Phishing works:
The SMS Anti-Phishing Solution can be used in conjunction with an SMS firewall or as a standalone solution for SMS phishing and Flubot attacks.
Every SMS is checked for the presence of a URL. Cellusys authenticates every URL against the Phishing Threat Intelligence Database registry. Even if the URL redirects multiple times across multiple domains, the destination URL will be authenticated:
The subscriber receives the message in one of three ways:
- Verified Safe URLs: Subscriber can open the link
- Potentially Dangerous URLs that cannot be verified: the link is replaced with a redirect link to a warning page explaining why the page is blocked, and urging the subscriber only to open with extreme caution.
- Dangerous URLs that are known: the link is replaced with a redirect link to a warning page explaining why the page has been blocked.
More Information about Fraud Insight solution for Malware
Sources:
https://www.proofpoint.com/us/threat-reference/smishing
https://www.juniperresearch.com/press/operator-a2p-messaging-revenues-62-billion-2023
Tags: Flubot, flubot solution, malware, smishing, trojan, zero trustCategorised in: Blog
